IT/OT Operations Lifecycle
Automating Infrastructure from Provisioning to Continuous Operations with UPTR™.
From Provisioning to Continuous Operations.
Operating modern IT and OT infrastructures is no longer a static task.
Industrial environments, logistics platforms, and critical infrastructure depend on systems that must remain secure, reproducible and continuously operational.
However, the operational lifecycle of these systems has become increasingly complex due to …
➜ heterogeneous hardware environments
➜ distributed edge infrastructure
➜ continuous software updates
➜ rising cybersecurity requirements
➜ regulatory pressure in critical infrastructure environments
Without a structured operational lifecycle, infrastructure gradually drifts away from its intended state.
Configurations diverge, updates become risky, and manual processes introduce operational uncertainty.
The IT/OT Operations Lifecycle describes a systematic approach to managing infrastructure from initial provisioning to long-term operation, ensuring systems remain stable, secure and reproducible.
Platforms such as UPTR™ enable organizations to automate this lifecycle and maintain a transparent and controllable operational state across IT and OT environments.
The IT/OT Operations Lifecycle defines the processes required to manage infrastructure throughout its entire lifespan:
- Provisioning infrastructure
- Applying reproducible configuration
- Operating systems and workloads
- Managing updates and patches
- Maintaining governance and compliance
- Ensuring resilience and recovery
In traditional environments these tasks are handled by separate tools and manual procedures.
The result:
➜ fragmented operational processes
➜ configuration drift
➜ update failures
➜ increasing operational risk
A lifecycle-driven approach consolidates these processes into a structured and automated operational model.
The Core Phases of the IT/OT Operations Lifecycle.
1. Infrastructure Provisioning
The lifecycle begins with reproducible system provisioning.
In industrial and edge environments, systems must often be deployed across hundreds or thousands of locations. Manual provisioning quickly becomes impractical and error-prone.
Automated provisioning ensures that systems start from a defined and reproducible baseline, including:
➜ operating system installation
➜ hardware initialization
➜ network configuration
➜ platform components
Modern provisioning mechanisms rely on image-based deployment and immutable operating systems, ensuring every node starts from the same trusted foundation.
2. Configuration Management
Once infrastructure is provisioned, it must be configured in a consistent and reproducible way.
Configuration management defines:
➜ system roles
➜ installed services
➜ network parameters
➜ security policies ➜ workload configuration
Tools such as Ansible enable infrastructure to be described as code, allowing configuration states to be versioned, audited, and automatically applied.
This approach eliminates configuration drift and enables teams to rebuild systems predictably and reliably.
➜ Related topic: Reliable infrastructure through reproducible configuration
3. System Operations
Operating systems and services must remain stable throughout daily operations.
Operational challenges typically include:
➜ monitoring infrastructure health
➜ scaling workloads
➜ managing distributed environments
➜ maintaining operational transparency
In IT/OT environments, these challenges are amplified by long hardware lifecycles, remote locations, and strict availability requirements.
Lifecycle-based operations ensure that infrastructure remains aligned with its intended state even as workloads evolve.
4. Update Management
One of the most critical phases of the operational lifecycle is update management.
Updates are necessary for:
➜ security patches
➜ feature improvements
➜ compliance requirements
However, updates can also introduce significant operational risk. Recent large-scale incidents have shown how a faulty update can disrupt global IT systems within minutes.
For organizations operating industrial or critical infrastructure environments, uncontrolled updates can lead to:
➜ production downtime
➜ operational disruption
➜ safety risks
A controlled update lifecycle includes:
➜ staged rollouts
➜ validation environments
➜ automated deployment pipelines
➜ rollback capabilities
➜ Related topic: Update Management for Critical Infrastructure
5. Governance and Compliance
Infrastructure operations must comply with internal governance rules and regulatory requirements.
This is especially relevant in sectors such as:
➜ energy
➜ transportation
➜ manufacturing
➜ logistics
➜ public infrastructure
Governance processes include:
➜ configuration auditing
➜ software approval processes
➜ security policies
➜ compliance documentation
Lifecycle automation ensures that governance rules are embedded directly into operational processes, rather than enforced manually.
➜ Related topic: Infrastructure Governance and Lifecycle Control
6. Resilience and Recovery
No operational lifecycle is complete without mechanisms for failure recovery and system restoration.
Resilience strategies include:
➜ automated rollback mechanisms
➜ reproducible system states
➜ disaster recovery procedures
➜ infrastructure redeployment
Instead of repairing broken systems manually, modern operational models allow systems to be recreated from a known state.
This dramatically reduces recovery time and operational uncertainty.
Why the IT/OT Lifecycle Matters for Critical Infrastructure.
Organizations operating industrial or critical infrastructure systems face a unique operational challenge.
Their environments must remain:
➜ highly reliable
➜ secure against cyber threats
➜ operational for many years
➜ compliant with regulatory frameworks
Traditional IT operations were never designed for this level of operational stability.
The lifecycle approach addresses this gap by creating a predictable operational model where infrastructure can be managed as a controlled system rather than a collection of manually maintained machines.
Automation is essential for managing complex infrastructure environments.
Platforms such as UPTR integrate multiple lifecycle processes into a unified operational framework:
➜ automated provisioning
➜ configuration management
➜ lifecycle-controlled updates
➜ governance enforcement
➜ rollback and recovery
By automating these processes, organizations can maintain infrastructure in a transparent and reproducible operational state.
This is particularly valuable in distributed edge environments, where manual operations are impractical.
From Infrastructure Management to Lifecycle Engineering.
Modern infrastructure operations are evolving from reactive system administration toward lifecycle engineering.
Instead of reacting to operational problems, organizations define:
➜ desired system states
➜ automated operational processes
➜ controlled update strategies
➜ reproducible infrastructure environments
The result is a predictable and controllable IT/OT operating model.
The Future of IT/OT Infrastructure Operations:
As infrastructure environments continue to grow in complexity, lifecycle-driven operations will become the foundation of reliable infrastructure management.
Organizations that adopt lifecycle automation benefit from:
➜ reduced operational risk
➜ faster infrastructure deployment
➜ predictable system updates
➜ improved cybersecurity resilience
➜ simplified compliance
For industries where operational stability is critical, the IT/OT Operations Lifecycle is becoming an essential operational framework.
To understand how each phase contributes to stable infrastructure operations, explore the following topics:
➜ Reliable Infrastructure through Reproducible Configuration
➜ Update Management for Critical Infrastructure
➜ Immutable Infrastructure
➜ Infrastructure Governance
➜ Automated Provisioning
➜ Operational Resilience and Recovery
Together, these components form the foundation of a modern lifecycle-driven IT/OT operations strategy.
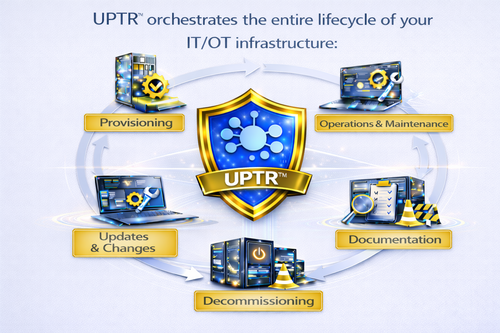
UPTR™ from LibOnIce orchestrates the entire lifecycle of your Linux-based IT/OT infrastructure.
It is not just another tool — and it does not replace your existing automation stack. Instead, it connects, standardizes and orchestrates it. While individual tools continue to handle specific tasks, UPTR™ ensures your entire operation works as one coherent system — from bare metal to application lifecycle.
The result: more resilience, more control, lower risk — and an operations platform that scales with your business.
What makes UPTR™ unique:
✔️ holistic approach (Provisioning + Lifecycle Management + DevOps)
✔️ open, security-first architecture based on open source principles
✔️ Compliance-ready for NIS2 / KRITIS requirements
✔️ Vendor-neutral – maximum control and long-term flexibility for customers
👉 With UPTR™, operations become a strategic asset instead of a daily firefighting exercise.
Linux based Lifecycle Management and DevOps integration for IT/OT infrastructures with UPTR™
From Raw System to Controlled Infrastructure
When a new IT system arrives, it has no identity, no network presence, no policy. UPTR™ takes control — and orchestrates the entire lifecycle: from provisioning to decommissioning.
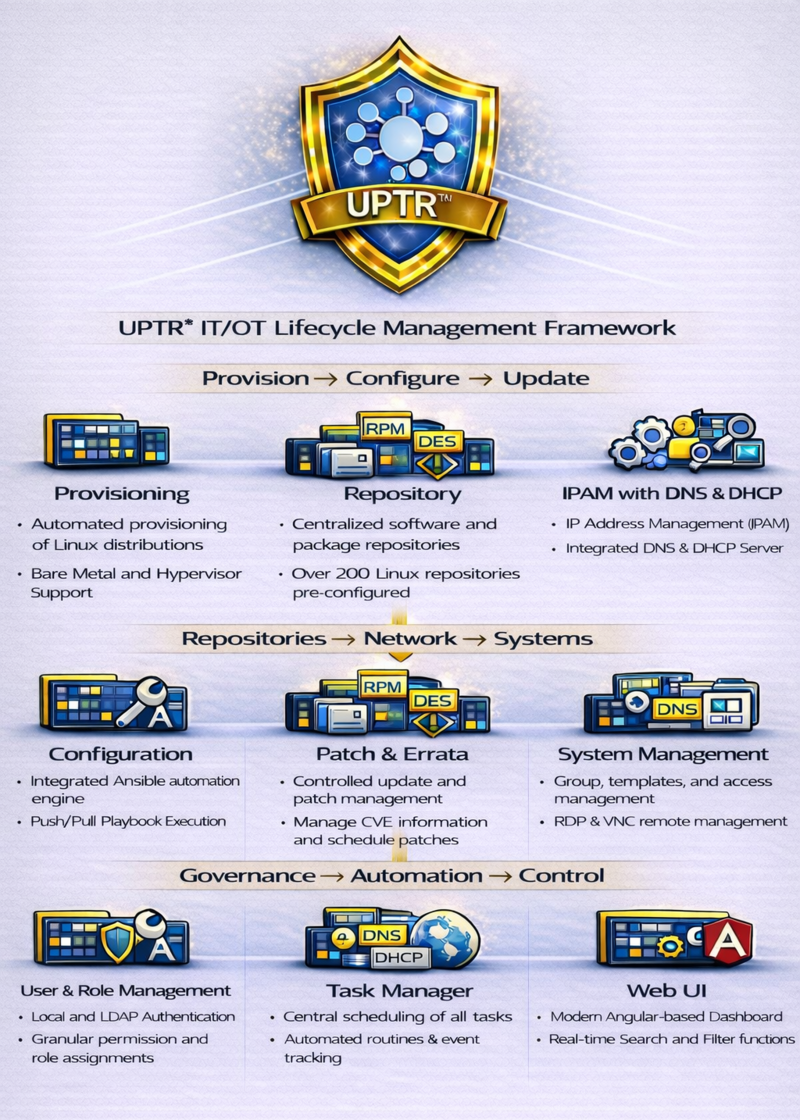
1) Provisioning — From Bare Metal to Productive Node
Everything must be reproducible, automated, and clean — whether rack server, edge node or VM.
Infrastructure & OS Support:
➜ Broad Linux coverage: AlmaLinux, CentOS, Debian, Fedora, Oracle Linux, RHEL, Rocky, SLES, Ubuntu
➜ Bare metal & virtualization: Proxmox, (v)Sphere, oVirt, BMC integration
➜ Standardized install methods: AutoYaST, Kickstart, Preseed
Network Identity via Integrated IPAM:
The system gets its address, role, and policy context automatically:
➜ Subnet definition & IP assignment
➜ DNS integration (BIND, Active Directory, Infoblox)
➜ DHCP provisioning (einsmase, ISC DHCP)
No Snowflakes:
➜ Repository management with 200+ preconfigured Linux repositories
➜ Clean, policy-based software sourcing
➜ DNS/DHCP tightly integrated into provisioning
Control Layer:
➜ Modern Angular-based Web UI / Dashboard
2) Operations & Maintenance — Control instead of Chaos
Once productive, installation turns into accountability: availability, security, traceability. In IT/OT environments, downtime is not theoretical — it is expensive.
System Management:
➜ Template-based governance
➜ Static & dynamic groups (manage fleets as fleets)
➜ VNC access & host attributes
➜ Powerful search & filtering across large estates
Task & Automation Control:
➜ Centralized task management
➜ Quartz scheduler (email alerts, recurrence, time-based control)
➜ Full task history & event monitoring — audit-ready traceability
3) Updates & Changes — When Routine Becomes Risk
Vulnerabilities. Compliance requirements. New releases. Updates are inevitable — uncontrolled updates cause outages.
Patch & Errata establishes control:
➜ Packages (RPM, DEB coming soon)
➜ Errata and CVE transparency
➜ Host-based patch planning and execution
You don’t patch ‘at some point’. You patch against defined hosts - with CVE context and full errata traceability.
4) Documentation — Making Knowledge Reliable
A system without documentation is like an industrial plant without wiring diagrams: It works — until it doesn’t. UPTR™ structures your configuration reality. Changes become traceable, versioned, and reproducible.
Configuration includes:
➜ Integrated Ansible support
➜ Online playbook editor
➜ Push/Pull mechanisms
Documentation becomes operational: Playbooks, processes, standards — not scattered notes.
User & Role Management ensures accountability:
➜ Local or LDAP authentication
➜ Roles such as Administrator, Manager, Admin
5) Decommissioning — Clean Shutdown, No Residual Risk
Every system reaches its end: Hardware refresh, site consolidation, project closure.
This is where critical mistakes occur:
➜ Orphaned DNS records
➜ Lingering DHCP leases
➜ Forgotten accounts
➜ Unclear ownership
With UPTR™, decommissioning becomes a defined lifecycle step:
➜ Task execution and audit via Task Manager (including history & monitoring)
➜ Access revocation through User & Role Management
➜ Network cleanup via IPAM with controlled DNS and DHCP processes